While distributed teams are on the rise, some leaders are hesitant to embrace remote because of the perceived security risks. Employees accessing company data on public wifi at a coffee shop in Bali is a chief security officer’s worst nightmare. But remote work is here to stay.
Companies need to find ways to allow location flexibility while also keeping data safe. Though there’s a lot that’s done on an infrastructure level to keep customer data secure, the truth is your company’s data is only as secure as the weakest individual link.
As long as our devices are online, we’re at risk. From laptops to kitchen appliances and home assistants, new devices come online every day, most lacking long-term support from their manufacturers. According to Have I Been Pwned (HIBP), 130+ million individual accounts have been breached across 400+ services for a total of 9+ billion times. And even though these numbers look daunting, they just scratch the surface. They miss breaches that have never been discovered or made public, targeted attacks, and everyday social engineering. What’s known is just the tip of the iceberg.
At our own fully remote company Doist, our internal guidelines have always been very simple. We only onboard new people a few times per year, most of whom are very tech-savvy. The need for more thorough guidelines was not apparent for a long time. It wasn’t until NordVPN was hacked that we started a more serious discussion about the topic, and worked together to craft a set of guidelines that would better protect us.
This article will focus on the minimum steps individual remote employees should take to safeguard their company’s data (not to mention their own personal data). While these security measures are valid for anyone, they’re especially important for remote companies with employees working from and traveling to anywhere in the world.
Encrypt your devices
Encryption helps prevent unauthorized access to the data on your devices. It does this by encoding the information in a way that makes it difficult to be deciphered by unauthorized people. This can be especially important in case of a lost or stolen device, as it helps prevent strangers from accessing your data without your password or pin.
Here’s how to turn on encryption on your device:
- Windows: Enable BitLocker.
- macOS: Enable FileVault.
- Linux: Use dm-crypt or similar.
- Android: Enabled by default since Android 6. Don’t use an earlier version (see below).
- iOS: Enabled by default since iOS 8. Don’t use an earlier version (see below).
Use supported versions of your device’s operating system
Even though operating system developers only support the last few major versions, security vulnerabilities are discovered frequently and can affect all and any version, supported or not. Unsupported versions don’t get security patches for vulnerabilities that are disclosed, putting your data at risk. It’s important to ensure you are using a supported version, ideally the latest one.

Here’s how:
- Windows: Check this list every once in a while.
- macOS: Apple is not transparent about its policy for macOS. Historically, security updates target the most recent major version and the 2 prior. For instance, if the current version is macOS Catalina, that means macOS High Sierra and newer versions are supported.
- Linux: Most active distributions are well supported.
- Android: Security updates target the current and last 2 major versions. For instance, if the current version is Android 10, that means Android 8 and newer versions are supported. In Android’s case, you must also ensure that your manufacturer/carrier is seeding the periodic security patches to your device. You should be getting them at least every few months. If not, consider upgrading, or checking if LineageOS has official support for your device.
- iOS: Apple is not transparent about its policy for iOS, either. Historically, security updates target the most recent major version and the 3 prior. For instance, if the current version is iOS 13, that means that iOS 10 and newer versions are supported.
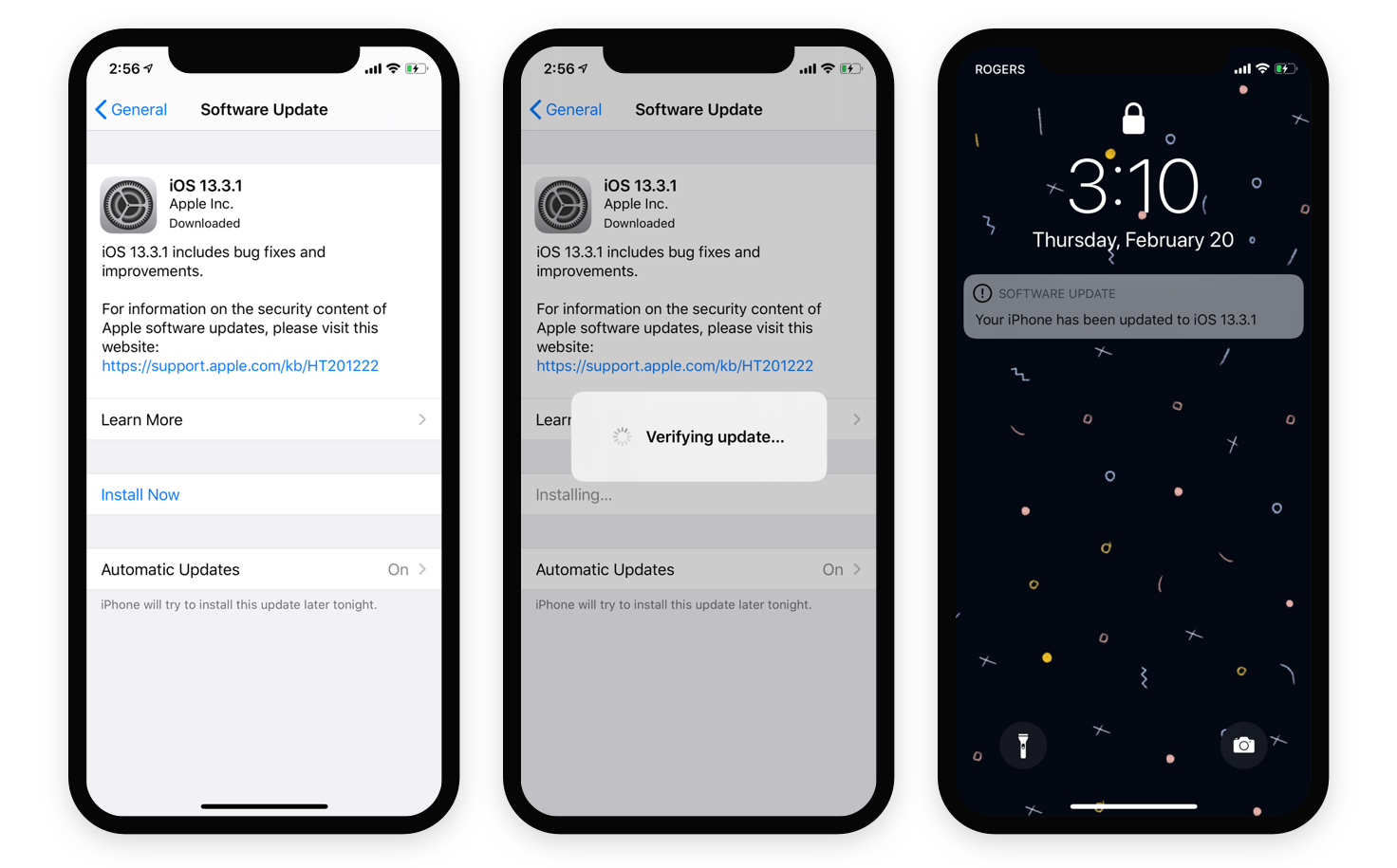
Keep the operating system up-to-date
The average time from the disclosure of a security vulnerability to its resolution is over 2 months. That’s a significant window of exposure even in the best-case scenario, and it’s in your best interest to not delay the process further. To get security patches as quickly as possible, ensure your device has automatic updates turned on and that you frequently apply them.
Automatic updates are enabled by default on most modern devices.
Keep your software up-to-date
The layer after the operating system is the software it runs, such as the browser or office suite. They, too, can be vulnerable. For the same reasons outlined above, it’s important to keep your applications up-to-date.
Most modern software checks for and applies or prompts to apply updates automatically. For everything else, make sure to periodically check that you’re using the latest version.
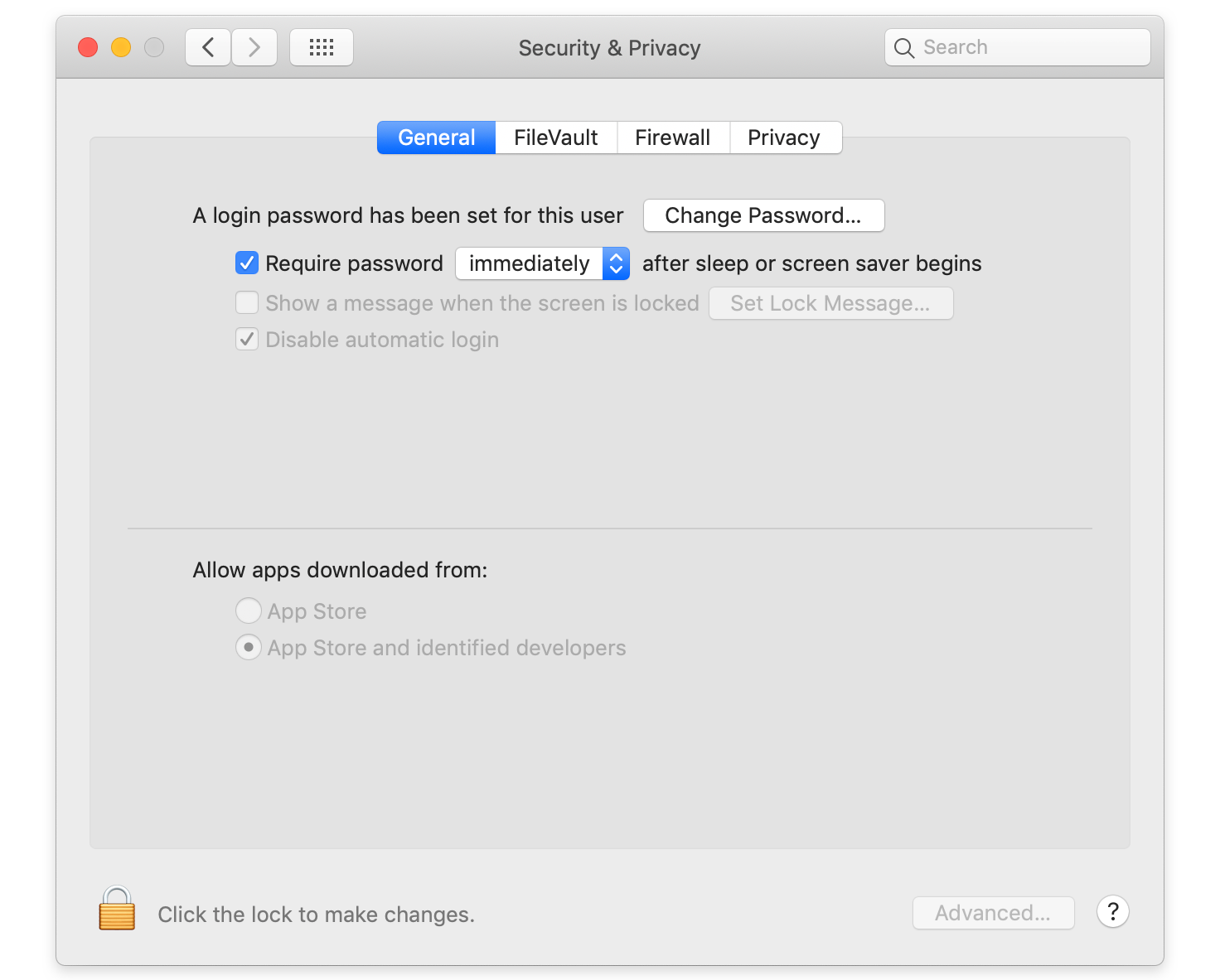
Disable automatic login
Unattended devices are easy targets for prying eyes unless they’re set up to ensure that you and only you can access them. To this end, you should ensure that automatic login is disabled and that a password, pin, or a biometric alternative is required when turning them on or resuming from sleep. Note that sharing your password or pin with others defeats the purpose, so you must keep them to yourself.
Automatic login is disabled by default on most modern devices.
Enable automatic locking
If you walk away from your device at your coworking space or the coffee shop you’ve been working from, you should lock it. But to err is human, and we can forget. When we do, automatic locking is there to help protect our devices from unintended access.
Make sure to configure an amount of time that, while convenient, is not unreasonably long, such as 30 seconds for mobile devices or 5 minutes for laptops.
Automatic lock is enabled by default on most modern devices.
Use a pin/password on your devices that is hard to guess
All this precaution is at risk if the pin/password to your devices is easy to guess. Make sure to avoid anything that’s easy to try, such as repeating the same number (e.g. 000000), sequences (e.g. 123456), and so on. Check lists of the common passwords to ensure you’re not using something that’s easy to guess.
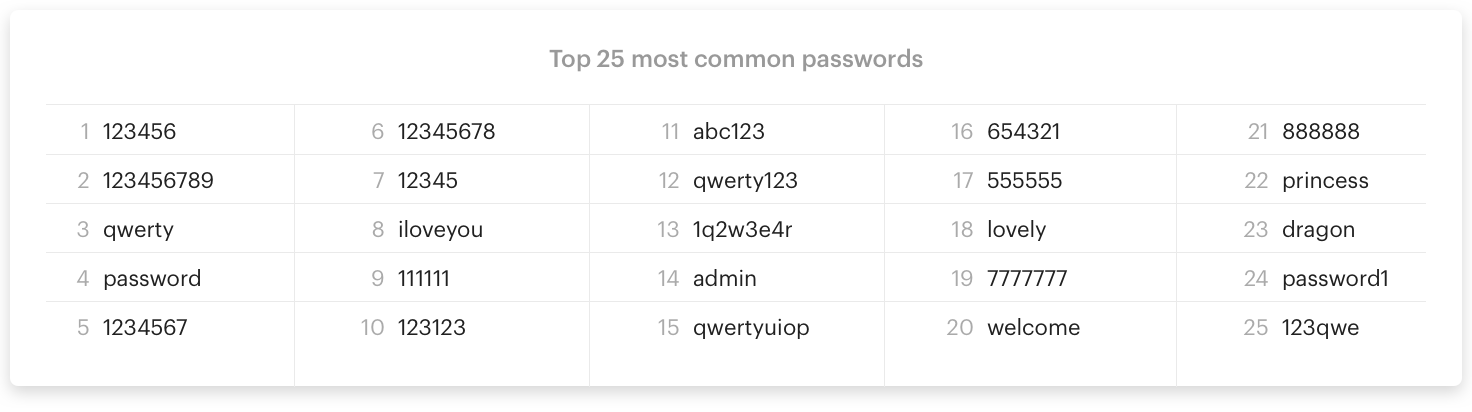
On top of this, avoid anything that’s related with you, such as your birth date, your license plate, your door number, etc. A good pin/password should look random to anyone that’s not you (if you test out this assumption, be sure to change your password immediately afterwards).

Use a password manager
Generally, you don’t want others to know or be able to guess your passwords or pins. And if someone does access one of them, you don’t want them to have access to more than a single device, application, or website. To keep your data safe, all of your passwords and pins should be unique, appropriately difficult, and be reset periodically. Managing this manually can be extremely cumbersome.
Password managers handle all of this for you. They help you create strong passwords and remember them, as well as share them with family members or friends securely. Most also help you store secure notes, credit card details, and other types of sensitive information. Some even ease your adoption of two-factor authentication (see next point). Password managers automate and simplify a lot of the tedious yet necessary grunt work around password hygiene. They’re a must-have.
At Doist, we recommend Bitwarden. There are many reasons we like it, such as its robust feature set for both free and paid plans, being open source, allowing users to run the server themselves if they want, and having undergone and published a security audit.
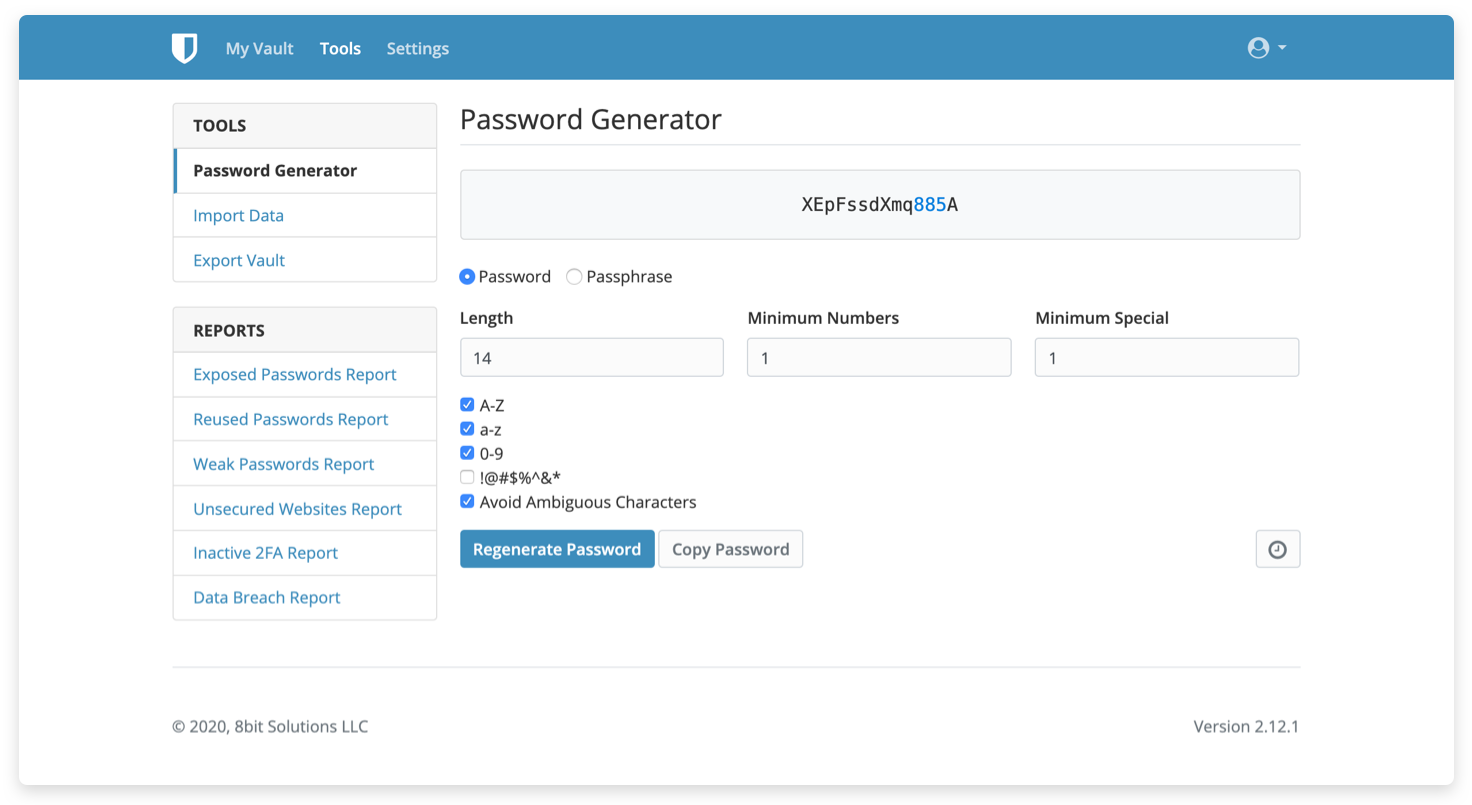
Despite our preference, it’s hard to go wrong with any popular option that is available across different platforms and doesn’t impose limitations on the number of devices or passwords you can store, such as 1Password or LastPass.
Enable two-factor authentication & use an authenticator app
Two-factor authentication means using two different factors to verify your identity to an app or site. The first and most common is your password. The second can take many forms but is typically a one-time code.
It’s important to be aware of safe and unsafe choices for the second factor. For instance, SMS is a popular option, but it’s been proven to be insecure, to the point that governments are explicit about its disapproval. Best practice is to use an authenticator app like Google Authenticator or Authy.
Regardless of this caveat, having two-factor authentication enabled drastically reduces the chances of fraud, data loss, or identity theft. An attacker can no longer pretend to be you by just knowing your password. They would also need access to whatever is generating your one-time codes, such as your authenticator app or security key.

Having two-factor authentication enabled is essential for everything holding sensitive data, such as your password manager, email, online banking, file and document hosting, etc. When in doubt, enable it. Better yet, enable it everywhere.
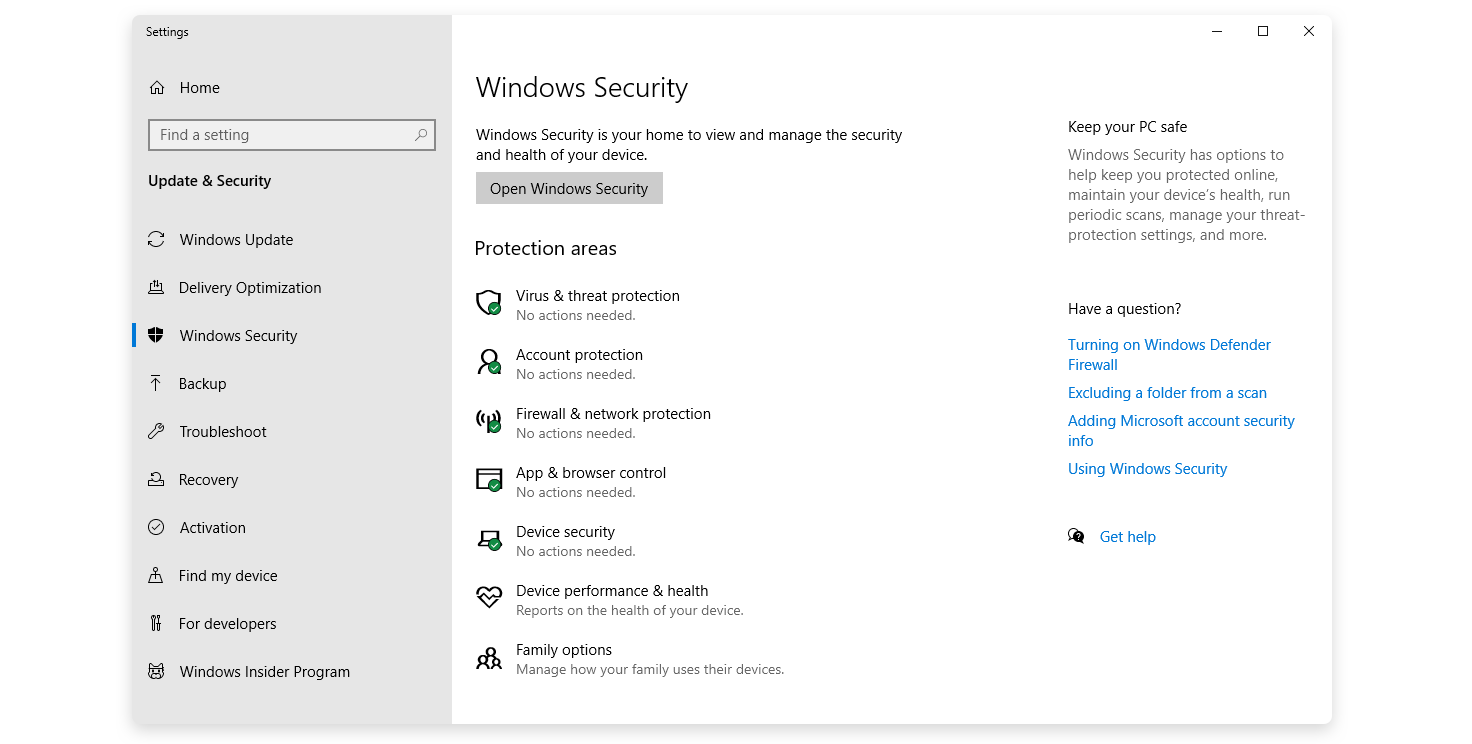
Enable find my device and remote wipe
Being able to locate and wipe devices remotely can be crucial in some situations, such as when a device is lost or stolen. Wiping, in particular, makes it much harder to access your data, no matter how much time or determination an attacker has. You can’t enable this without access to your device, so if you haven’t done it before, now would be the best time.
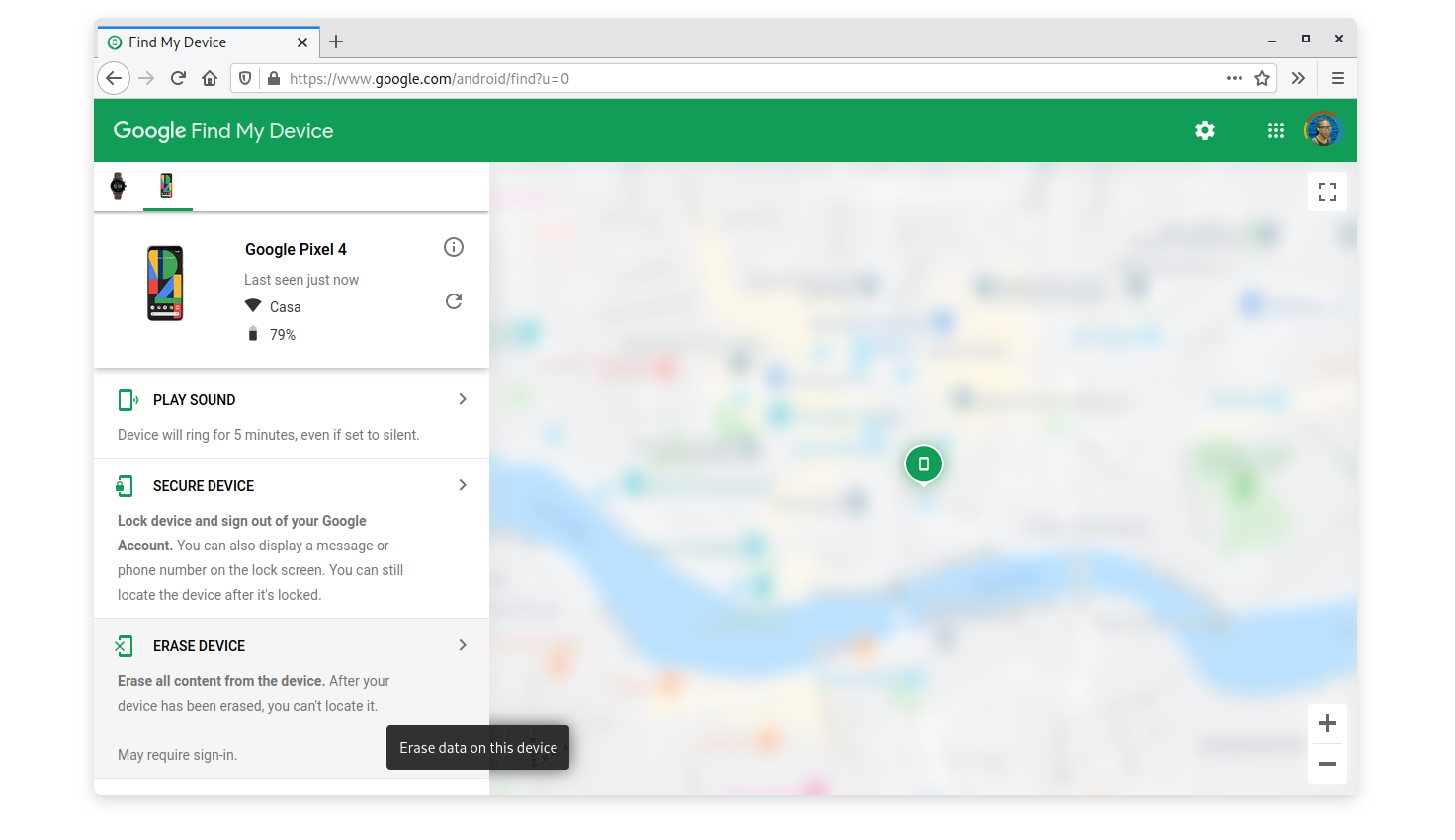
Here’s how:
- Windows: Enable in Settings > Update & Security > Find my device.
- macOS: Setup iCloud on your device. Enable via Settings > Your Name > iCloud > Find My Mac.
- Linux: Requires a third-party application, but we don’t have any specific recommendation.
- Android: Set up a Google account on your device. It’ll then be enabled by default.
- iOS: Setup iCloud on your device. Enable via Settings > Your Name > iCloud > Find My iPhone/iPad.
Wipe any device you dispose of
When lending, giving, selling, or trashing a device, it’s important to wipe it and reset it to factory settings. Doing so prevents your data from being accessed after you no longer have control over your device, temporarily or permanently.
Before doing this, remember that wiping deletes all of the information on the device. Back it up if you think you’ll need it in the future or if you’re unsure.
Here’s how:
- Windows: Follow Microsoft’s guide. When asked, select Remove everything.
- macOS: Follow Apple’s guide.
- Linux: Follow Arch’s guide, and then reinstall your distro.
- Android: Go into Settings > System > Reset options > Erase all data (factory reset).
- iOS: Follow Apple’s guide.
Use a VPN in public or untrusted networks
A VPN establishes a secure and encrypted connection to another network over the Internet and routes your traffic through it. Doing this substantially improves your online privacy and anonymity. It makes it extremely difficult for attackers on your network to snoop on your traffic and intercept what you are doing. It also prevents websites from knowing your real location, or your internet provider from monitoring your activity or using traffic shaping on your connection. The list goes on.
If not illegal in your country, ensure you use a VPN in public networks or networks you don’t trust such as co-working spaces, coffee shops, restaurants, airports, etc. You’re welcome to go a step further and use a VPN all the time.
At Doist, we recommend Mullvad. We like it for its transparency as well as its unique take on privacy and security. The company allows its users to remain completely anonymous, even to them—they don’t rely on email addresses and allow users to pay using cryptocurrencies or to mail them money. It has also undergone and published a security audit.
Use your best judgment
Unfortunately, online privacy and security does not boil down to following a fixed set of guidelines. Being protected can be situational, and you’ll often have to use your best judgement.
Examples include:
- Don’t open email attachments if you don’t know and trust the sender.
- Don’t execute downloaded files, unless you are sure their source is trustworthy.
- Prefer applications from your vendor’s official store or repositories, such as the Windows Store, Apple Store, or Google Play. In these stores, applications undergo a review process, which helps ensure they are harmless and haven’t been tampered with.
- Avoid plugins for browsers or other programs, unless you are sure their source is trustworthy.
- Never click through browser or operating system warnings without reviewing them properly.
Truth be told, this last section encompasses all others. Be cautious of how you use your devices, be skeptical and preventative, and use your best judgment.
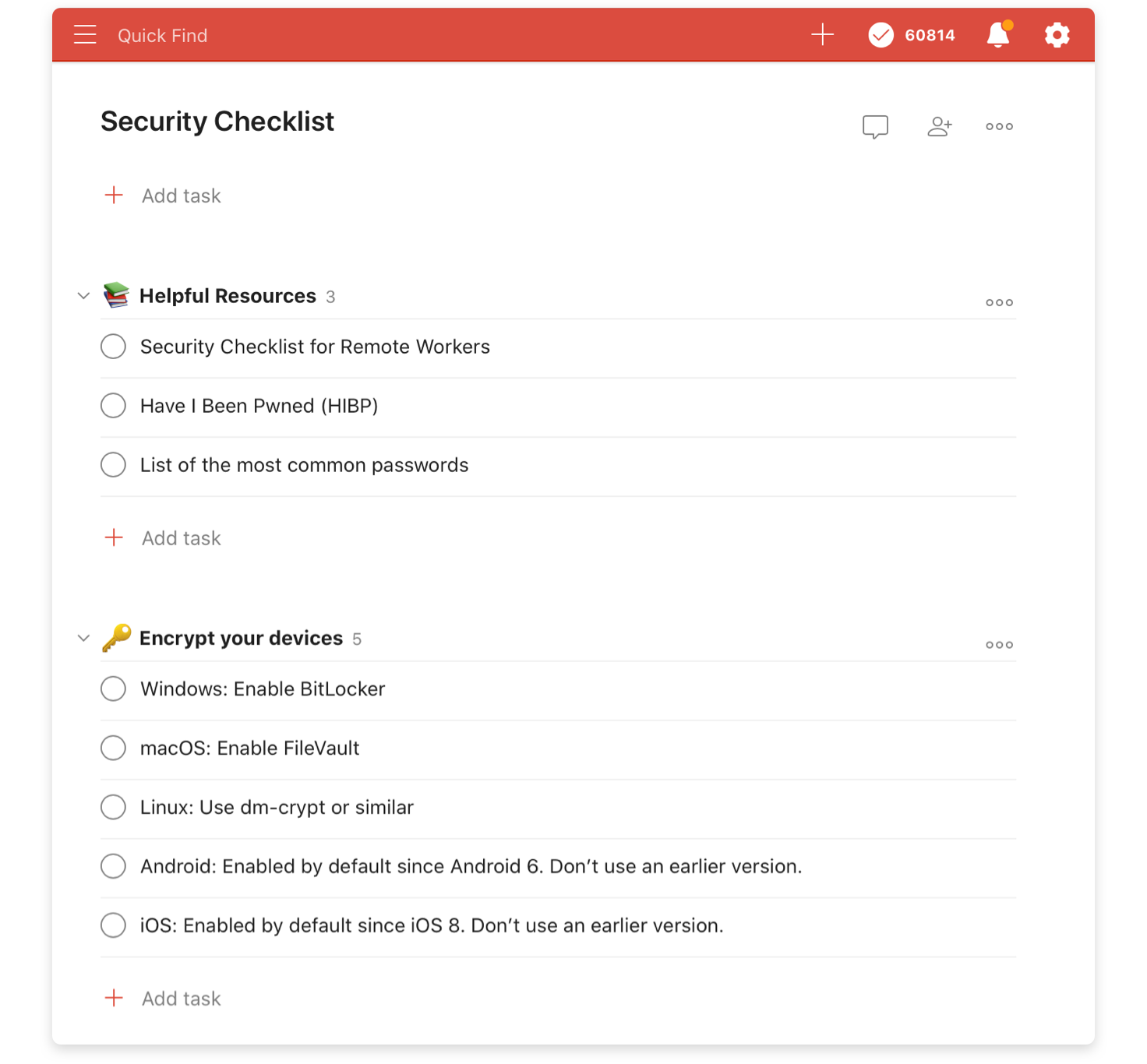
We’ve created a Security Checklist Todoist template to make it easier to keep your information secure. Use it yourself and share the link with your team to ensure that everyone is following best security practices.
In the end, it doesn’t matter if we’re Jane Doe or Jeff Bezos. It doesn’t matter if it’s just our data or our team’s. It’s paramount that we secure our devices by following best practices in keeping our private information private.
Luckily, maintaining good online hygiene is not very complicated. A few one-off actions and a handful of simple habits can go a long way. While there are no silver bullets when it comes to data security, the steps above will allow you to improve your privacy and safety online.